The RV042 is a Dual WAN, 4 port switch, VPN Router. Work just got it in to do a little load balancing and for fail over protection. One of my favorite things to do with new toys like this guy is give them a nice once over. Which of course is how i found a XSS in the login logging functions of this device. I was originally looking for weaknesses in the login scheme and notice that my attempts are being logged, notably the user name i was trying to login as was being logged, along with a brief description of the failure. I then put non-standard characters in there which broke the UI, after some more playing around i found i was able to get html to render, from there i just started messing with XSS payloads till i found one that worked.
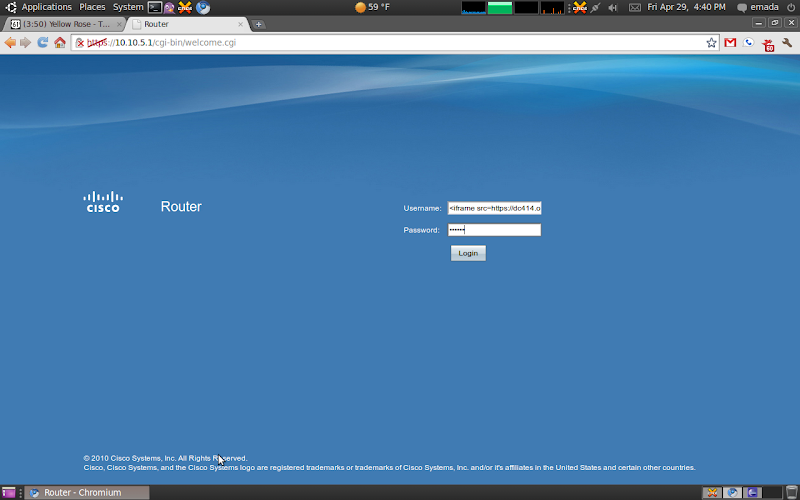
Here is my working XSS at the login screen:
The string i used is < iframe src="https://new.dc414.org" >
For password i just put in some junk
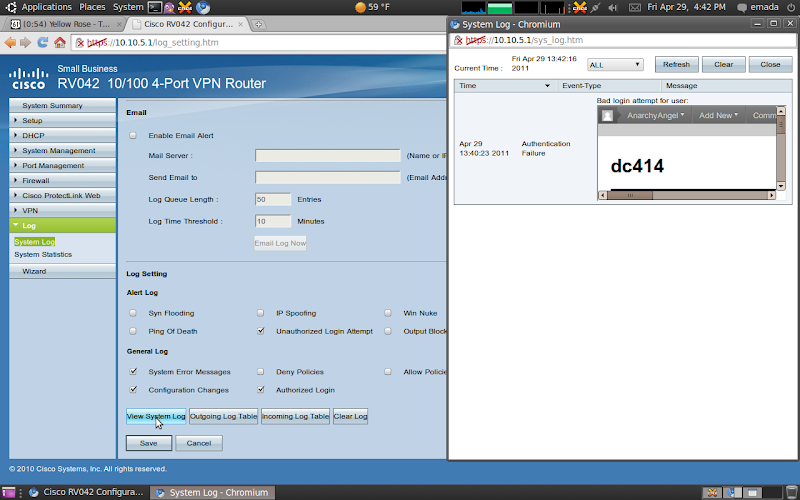
Here is what it looks like after i submit:

Here is the XSS in action 🙂
K thats it, enjoy, peace.

Great find on the XSS vulnerability! I’m curious, though, if this RV042 is the same hardware as the older RV042s, because you seem to be running an aesthetically pleasing interface as opposed to the ugly old Linksys configuration. What firmware revision is yours running? I’m wondering if the firmware from yours would work with ours.
Again, great work!
Thanks, and I don’t know if its the same hardware as RV042s. The firmware I was using in this post was v4.0.0.07-tm
If you’re running v4.0.0.07-tm, you have the newest hardware version.