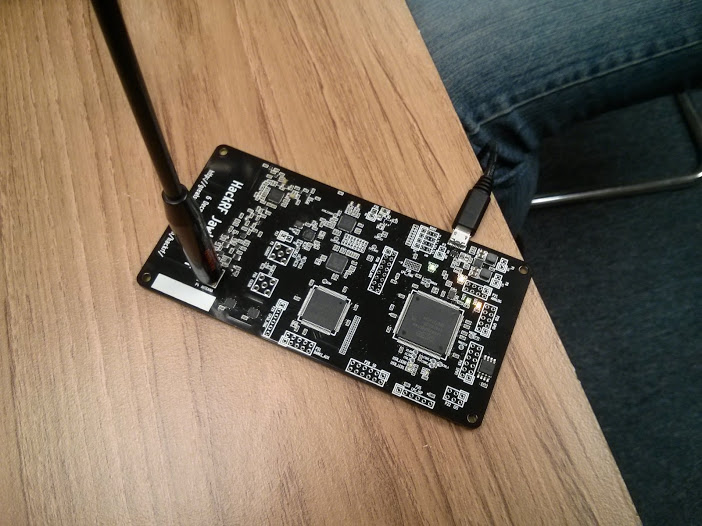
We’re still very much alive and active, no one has bothered to update the website is all. 🙂 dw5304 got us off to a fun start with some Outernet reception, although it was really a demofail. Still fun to set up a satellite and receive signals!
Klaiviel had an awesome 3d printed brute force machine in the works for combination locks. Very fast!
We also did a nice sized LAN party on Saturday, lots of fun, booze, and yelling commenced. Want to join in the fun? Feeling like you missed out? Are you on our mailing list? You should be! or join us on IRC on freenode at #dc414.
-darkwind



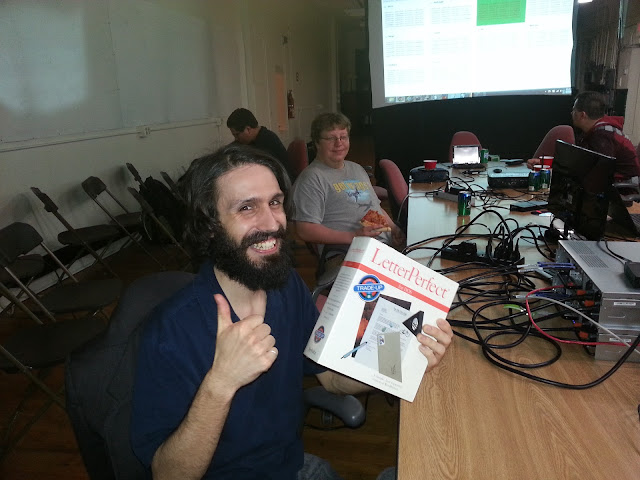 edgewalker was one of the lucky contestants to win the Free Junk Giveaway. Enjoy the LetterPerfect software on your IBM/DOS compatible PC!
edgewalker was one of the lucky contestants to win the Free Junk Giveaway. Enjoy the LetterPerfect software on your IBM/DOS compatible PC!