February was another great meeting. It started with me and ngharo running late then doing the introductions, which there was a lot of. Its always good to see new faces at meetings. Then I broke the sad news that I will be leaving Wisconsin and so dc414 as well, appointed ngharo as new prez and stepped down. Then ngharo said a few words and gave us a glimpse of some of the changes he will be making. Everyone be sure to congratulate ngharo, I can’t wait to see what he does with the place.
Rob started the demos off with hacking a used disposable flash camera and a halogen light bulb to make a handy improvised flash light. I perfect zombie apocalypse type hack. Then he busted out materials for everyone to make their own zombie caution light. It did’t take long for people to start hacking it up even more and did all kinds of crazy things. Vlad was the first to turn things up to 10 by doing something to the transformer in the camera to pump out more voltage and get a brighter light. Then dw5304 and others did their best to blow the capacitors and other things up! Then using the flash bulb that came with the camera and capacitors over 9000 we tried to do some UV tattooing. Next up was Klaiviel doing a key impressioning demo for the newbies in the crowd. Here are some photos of the meeting.
So here it is, my last post on dc414. It has been a fun ride and I will miss everyone. You can still find me on the dc414 irc chan and I will be at meetings via G+ or what ever ngharo sets up for the group. See you out there.
-AA

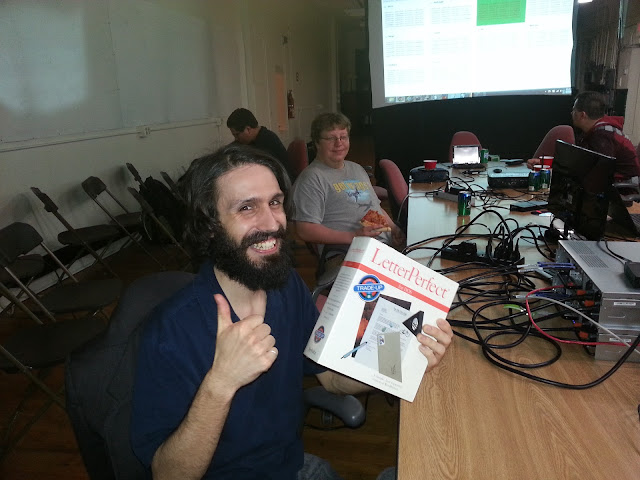 edgewalker was one of the lucky contestants to win the Free Junk Giveaway. Enjoy the LetterPerfect software on your IBM/DOS compatible PC!
edgewalker was one of the lucky contestants to win the Free Junk Giveaway. Enjoy the LetterPerfect software on your IBM/DOS compatible PC! 