So I have this nice new computer that I built with a asus p9x79 motherboard. I wanted it to become a 2012 server for some stuff. After loading the OS I found out that the nic is “incompatible” seeing intel thinks that its a desktop board and should not be used in a server. I went looking though the inf file and found out that it was ignoring the hardware id’s.
[ControlFlags]
ExcludeFromSelect = \
PCI\VEN_8086&DEV_1502,\
PCI\VEN_8086&DEV_1503
Well this sucks…. lets fix it.
I then removed the exludefromselect and the two lines fallowing it.
went to install the modified driver and ended up with 
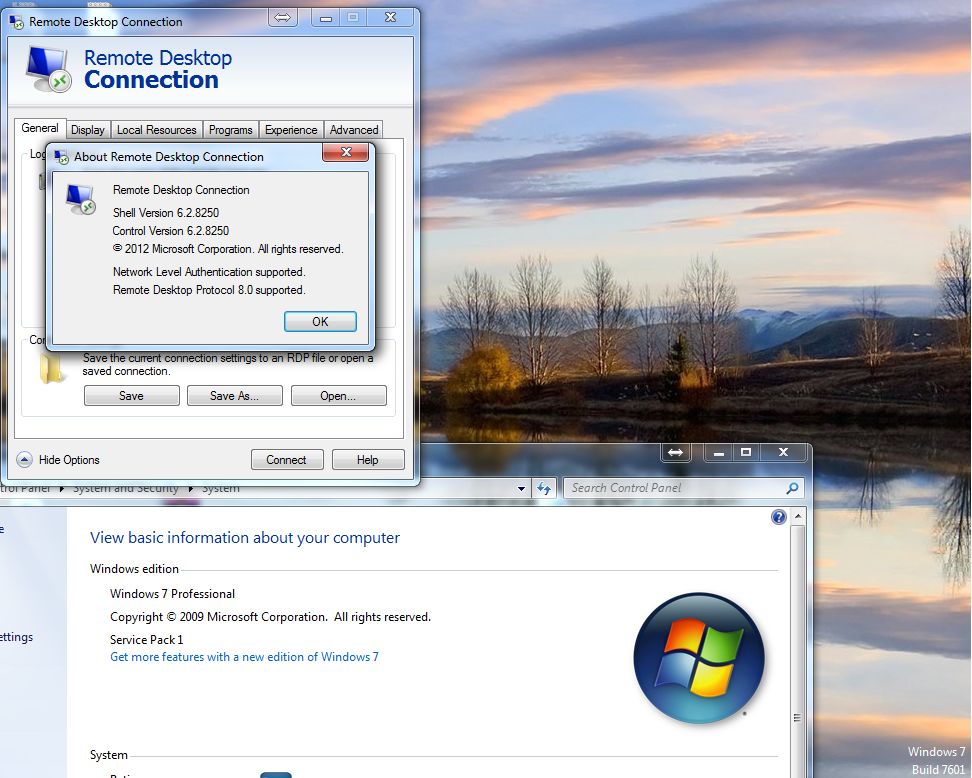
well at least I know its ok :). Now lets fix the catalog’s hash.
A hunt on google told me I needed inf2cat so lets download it here.
inf2cat /driver:”C:\Driver” /os:8_X64
My new catalog was created :).
went and tried installing my new driver once again and Damm :(… digital signature is missing wtf???? how the hell am I going to fix that I thought.
A little more searching found out we can make a self signed cert and attach it to a driver “he he”…. nice try Microsoft…..
So lets get this sucker signed. download here
makecert -r -n "CN=Intelnic" -pe -ss MyCertStore -sr LocalMachine
Now I needed to export this cert with its private key so we can import it into “Trusted Root CAs” and “Trusted Publishers” on my local machine I was creating the driver and also on the target machine I wanted to install my driver at :).
Now that we have it imported lets sign this sucker.
signtool sign /s MyCertStore /n "Intelnic" /t http://timestamp.verisign.com/scripts/timestamp.dll "C:\Driver\e1c63x64.cat"
Went back to my server installed the cert int trusted root cas and trusted publishers hey look my nic now works :).

Thanks Microsoft for making a “secure” os that has to have drivers that are signed … but wait…. I just made it my self o well there went that idea….