At the last meeting I showed everyone how to use a format string vulnerability in a password storage app to bypass the master password and pull data out of memory. That is just one way to exploit this type of vulnerability so I challanged everyone at the meeting to get the app I used “code below” to execute their supplied input. The first person to let me know they got it and do a demo get $20! So it pays to be a little early.
#include < stdio.h >
#include < string.h >
int main (int argc, char *argv[])
{
char** spw = "dc414 pwnz";
char text[1025];
strcpy(text, argv[1]);
if (strcmp(text, "asd123")==0) {
printf("Correct the password is %s \n",spw);
return 0;
}
printf(text);
printf(" is wrong\n");
return 0;
}


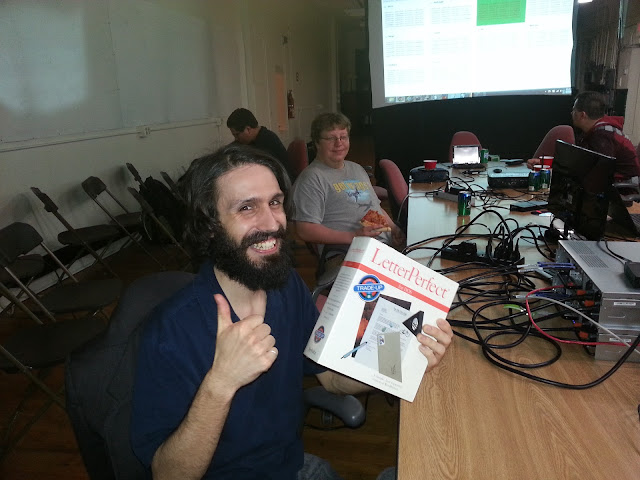 edgewalker was one of the lucky contestants to win the Free Junk Giveaway. Enjoy the LetterPerfect software on your IBM/DOS compatible PC!
edgewalker was one of the lucky contestants to win the Free Junk Giveaway. Enjoy the LetterPerfect software on your IBM/DOS compatible PC!