We have added a few achievements here and there and changed how you get badges. We also changed up the badge idea it self a little, now once you finish up the achievements for a badge you get a cloth badge for free and become eligible to buy an electronic badge. Work on the badges them selves are still in the design phase but it is coming along nicely, lots of great ideas flying around. Lastly, thanks to a awesome donation by Black Rat we now have wireless access points for the badge program! Ok that is it for now, get working on pwning your own badge and enjoy.
Monthly Archives: December 2011
dc414 hangout
Starting at the next meeting we will be streaming everything to the web via Google+ hangout! So even if you can’t make it to MKE you can still join the meeting. You wont be able to get in on any prize giveaways or beer drinking, but you can do some drinking of you own and you can of course take part in the discussions. While it is free to join in on the fun we do ask that you give a few bucks via PayPal to help keep dc414 going. I hope to see you there 🙂
New Years Eve PARTY!!!!
dc414 is hacking up a party for new years and we want to see you there. We plan on getting drunk, blowing stuff up, playing some games, playing with a Tesla coil and who knows what else! There will be some free food and beer but don’t be a bitch, bring your own to share 🙂 The festivities will start around 7pm at ngharo’s place. Email anarchy at dc414 or the mailing list for more information. I will see you there!
dc414’s badge program project.
The badge program project is a little game for hackers, crackers, and phreaks. The goal is to facilitate learning in a fun and interesting way. Each badge has a list of achievements you must obtain to be eligible to get the badge. Some achievements will be as easy as clicking a like button for FB, another might be as hard as having to try and social engineer a password out of a random person. Every time you get a badge you also get a mystery prize!!
The badges them selves are still under development so expect future posts about them as we finish them up. For a list of the badges and their achievements go here. So get started and get your 1337 badge now!
December meeting recap
Decembers meeting was awesome! Vlad gave a great in depth wi-spy demo. He showed us what a Bluetooth file transfer looks like, what microwaves look like and access points looks like, and gave good detail of just what exactly was going on. Before the meeting he asked people to bring in any wireless devices to see what they looked like in wi-spy while operating. dw5304 came packing with a some directional wireless access points, one so powerful it completely took over the entire spectrum that wi-spy displays.
Then i gave my presentation on using sql injections to bypass logins to sites and admin areas. I showed what should be sent to the sql server, how it looks in php and how to identify exploits. Then showed what a sql injection looks like when passed to the server. I didn’t stop there, we broke into gmtoday.com to take a look at the news paper, then used a google dork to pwn a few more logins. I also talked about dc414’s new badge program project, more on this later, and announced dc414’s new year eve party! More on this later as well.
dw5304 finished off the presentations with a killer demonstration of just how weak time warners security is. He showed us how to take complete control of one of their cable modems with just a few requests, even how to build your own private proxy network made out of time warner modems! Then to top it off demoed a never ending DoS on a modem, kicking this client off line for as long as he wished!
Other then the normal junk i bring to give away, ngharo donated a portable dvd player for cars and F4r4d4y donated a arduino “thanx guys”. All of which went to a good home. Here are some pics cmoney took at the meeting “thanx cmoney”, and a big congrats to Castor for winning the anti-M$ poster and pantsme on snagging the arduino!
Castor and his winnings:

rootkit hidden in millions of cellphones
Another email just surfaced …
rootkit hidden in millions of cellphones
Rootkit found in Android, Symbian, BlackBerry, webOS and even iOS handsets …. but not windows phone’s
The rootkit belongs to a company called Carrier IQ and it seems that it has low-level access to the system that allows it to spy on pretty much everything that you do with your handset. This, on the face of it, seems like an extremely serious breach of security, privacy and trust.
The capabilities of the rootkit were first discovered by 25-year-old Trevor Eckhart.
Here’s a video showing how everything, including text messages and encrypted web searches, are being logged. It’s truly horrifying.
NOTE: At this point there is no evidence to suggest that keystroke data is being transmitted from the handset.
According to Carrier IQ the company is ‘not recording keystrokes or providing tracking tools.’ The video above seems to suggest otherwise.
When Eckhart initially labeled the software as a rootkit, Carrier IQ threatened him with legal action. Only when the Electronic Frontier Foundation stepped in did the company back off from this threat.
“Every button you press in the dialer before you call,” Eckhart says on the video, “it already gets sent off to the IQ application.”
Like I said earlier, there’s a version of Carrier IQ on Apple’s iOS, but it doesn’t seem to be quite the same and doesn’t seem to access as much information. Also, if you want to disable Carrier IQ on your iOS 5 device, turning off Diagnostics and Usage under Settings seems to be enough.
You might have noticed that I didn’t list Windows Phone 7 OS earlier. That’s because it seems that Windows Phone handsets don’t have Carrier IQ installed.
Here’s a video that explains some more about Carrier IQ. This video also contains a clip from a video by Carrier IQ’s vice president of marketing explaining how the company sees this as being completely legal.
[UPDATE: According to a statement from Apple to AllThingsD, Apple stopped supporting Carrier IQ with iOS 5.0:
“We stopped supporting Carrier IQ with iOS 5 in most of our products and will remove it completely in a future software update. With any diagnostic data sent to Apple, customers must actively opt-in to share this information, and if they do, the data is sent in an anonymous and encrypted form and does not include any personal information. We never recorded keystrokes, messages or any other personal information for diagnostic data and have no plans to ever do so.”
When begs the question … what’s collecting all the information on the iPhone? Is this a mechanism developed by Apple for Apple?]
Bit shocked that your iPhone has that Carrier IQ logging feature built into the OS? You can switch it off … in fact, I’ve shown you how to do this before!
Here’s how!
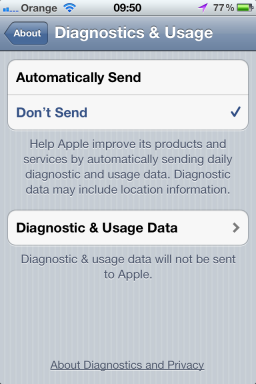
Buried in the Settings menu is an option to choose not to send what Apple calls ‘diagnostic and usage data.’ This option is buried real deep:
Settings > General > About > Diagnostics & Usage
Here’s the screen you’re looking for:
Set this to Don’t Send and you can stop worrying about where your data is going and who’s looking at it.
Note that this feature is only present on handsets running iOS 5.0 or later (so the iPhone 4S and upgraded iPhone 4 and 3GS handsets.
Microsoft Virtualization Event in Brookfield
Just got an email from Microsoft saying they have a virtualization event in brookefield.
Figured since I was going I’d share in case anyone else wants to join me. Should be worth while.
Starts: Thursday, December 08, 2011 9:00 AM
Ends: Thursday, December 08, 2011 5:00 PM
Time zone: (GMT-06:00) Central Time (US & Canada)
“Sheraton Milwaukee Brookfield
Brookfield Wisconsin 53005
United States
|
Register by Phone: 1-877-MSEVENT 9AM-7PM EST M-F
|
| Meal: Yes |
| Presenter(s): Brian Lewis and Matt Hester. |
| Language(s): English. |
| Product(s): Microsoft System Center Virtual Machine Manager, Windows Azure, Windows Server and Windows Server 2008 R2. |
| Audience(s): IT Generalist.”or register here |